标签:imp range utf-8 测试 观察 col 获取 base cdecl
测试文件:https://www.lanzous.com/i9la55a
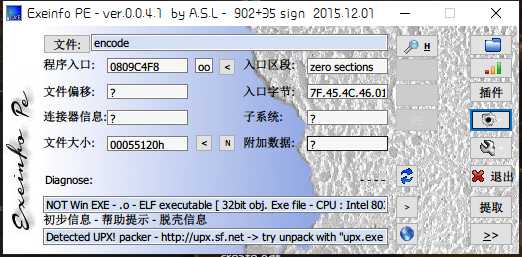
获取信息:
UPX脱壳后,IDA打开
int sub_804887C() { int v0; // eax int result; // eax int v2; // ecx unsigned int v3; // et1 unsigned int i; // [esp+Ch] [ebp-FCh] unsigned int v5; // [esp+10h] [ebp-F8h] unsigned int v6; // [esp+14h] [ebp-F4h] int v7; // [esp+1Ah] [ebp-EEh] int v8; // [esp+1Eh] [ebp-EAh] int v9; // [esp+22h] [ebp-E6h] int v10; // [esp+26h] [ebp-E2h] __int16 v11; // [esp+2Ah] [ebp-DEh] char v12[30]; // [esp+2Ch] [ebp-DCh] int v13; // [esp+4Ah] [ebp-BEh] int v14; // [esp+4Eh] [ebp-BAh] int v15; // [esp+52h] [ebp-B6h] int v16; // [esp+56h] [ebp-B2h] int v17; // [esp+5Ah] [ebp-AEh] int v18; // [esp+5Eh] [ebp-AAh] int v19; // [esp+62h] [ebp-A6h] int v20; // [esp+66h] [ebp-A2h] int v21; // [esp+6Ah] [ebp-9Eh] int v22; // [esp+6Eh] [ebp-9Ah] int v23; // [esp+72h] [ebp-96h] int v24; // [esp+76h] [ebp-92h] __int16 v25; // [esp+7Ah] [ebp-8Eh] char v26; // [esp+7Ch] [ebp-8Ch] unsigned int v27; // [esp+FCh] [ebp-Ch] v27 = __readgsdword(0x14u); v7 = ‘galF‘; v8 = ‘ihT{‘; v9 = ‘_a_s‘; v10 = ‘galF‘; v11 = ‘}‘; v5 = strlen(&v7); v13 = ‘8D8E‘; v14 = ‘19DB‘; v15 = ‘A178‘; v16 = ‘65E1‘; v17 = ‘F35F‘; v18 = ‘9884‘; v19 = ‘F286‘; v20 = ‘4169‘; v21 = ‘2FA2‘; v22 = ‘F8BA‘; v23 = ‘A7DE‘; v24 = ‘5DFC‘; v25 = ‘E‘; printf("Please input your flag:"); read(0, &v26, 256); if ( strlen(&v26) != 21 ) exit(0); v0 = sub_8048AC2((int)&v26); strcpy((int)v12, v0); v6 = length(v12); for ( i = 0; i < v6; ++i ) // 异或操作 v12[i] ^= *((_BYTE *)&v7 + i % v5); sub_8048E24(v12, v6, &v7, v5); if ( !strcmp(v12, &v13) ) exit(0); printf("right!"); result = 0; v3 = __readgsdword(0x14u); v2 = v3 ^ v27; if ( v3 != v27 ) sub_806FA00(v2); return result; }
很多未知函数,我们能够猜出是什么函数,在代码中已改。
在代码中,有两处函数我们不清楚作用。第一处
v0 = sub_8048AC2((int)&v26);
函数传入参数是我们输入的字符串,打开函数后
int __cdecl sub_8048AC2(int a1) { int v2; // [esp+8h] [ebp-20h] int v3; // [esp+Ch] [ebp-1Ch] int v4; // [esp+10h] [ebp-18h] int v5; // [esp+18h] [ebp-10h] int v6; // [esp+1Ch] [ebp-Ch] v5 = length(a1); if ( v5 % 3 ) v2 = 4 * (v5 / 3 + 1); else v2 = 4 * (v5 / 3); v6 = sub_80597A0(v2 + 1); *(_BYTE *)(v2 + v6) = 0; v3 = 0; v4 = 0; while ( v2 - 2 > v3 ) { *(_BYTE *)(v6 + v3) = a0123456789Abcd[(unsigned __int8)(*(_BYTE *)(v4 + a1) >> 2)]; *(_BYTE *)(v6 + v3 + 1) = a0123456789Abcd[16 * (*(_BYTE *)(v4 + a1) & 3) | (unsigned __int8)(*(_BYTE *)(v4 + 1 + a1) >> 4)]; *(_BYTE *)(v6 + v3 + 2) = a0123456789Abcd[4 * (*(_BYTE *)(v4 + 1 + a1) & 0xF) | (unsigned __int8)(*(_BYTE *)(v4 + 2 + a1) >> 6)]; *(_BYTE *)(v6 + v3 + 3) = a0123456789Abcd[*(_BYTE *)(v4 + 2 + a1) & 0x3F]; v4 += 3; v3 += 4; } if ( v5 % 3 == 1 ) { *(_BYTE *)(v3 - 2 + v6) = 61; *(_BYTE *)(v3 - 1 + v6) = 61; } else if ( v5 % 3 == 2 ) { *(_BYTE *)(v3 - 1 + v6) = 61; } return v6; }
.rodata:080BB9A8 a0123456789Abcd db ‘0123456789+/abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ‘,0
通过观察,这应该是一个变表的Base64加密
第二处
sub_8048E24((int)v10, v4, (int)&v5, v3)
unsigned int __cdecl sub_8048E24(int a1, unsigned int a2, int a3, int a4) { char v4; // ST2B_1 unsigned int result; // eax unsigned int v6; // et1 int v7; // [esp+1Ch] [ebp-11Ch] int v8; // [esp+20h] [ebp-118h] unsigned int i; // [esp+24h] [ebp-114h] char v10[256]; // [esp+2Ch] [ebp-10Ch] unsigned int v11; // [esp+12Ch] [ebp-Ch] v11 = __readgsdword(0x14u); sub_8048CC2((int)v10, a3, a4); LOBYTE(v7) = 0; LOBYTE(v8) = 0; for ( i = 0; i < a2; ++i ) { v7 = (unsigned __int8)(v7 + 1); v8 = (unsigned __int8)(v10[v7] + v8); v4 = v10[v7]; v10[v7] = v10[v8]; v10[v8] = v4; *(_BYTE *)(a1 + i) ^= v10[(unsigned __int8)(v10[v7] + v10[v8])]; } v6 = __readgsdword(0x14u); result = v6 ^ v11; if ( v6 != v11 ) sub_806FA00(); return result; }
这应该是一个RC4加密函数, sub_8048CC2((int)v10, a3, a4);函数是初始化函数
这样整个代码的思路就很明晰了,对输入字符串进行base64加密后,再进行异或操作,最后进行RC4加密(Key = "Flag{This_a_Flag}"),并与"E8D8BD91871A1E56F53F4889682F96142AF2AB8FED7ACFD5E"比较
解密网站:
http://tool.chacuo.net/cryptrc4
http://ctf.ssleye.com/rc4.html
http://tools.jb51.net/password/rc4_encode
https://gchq.github.io/CyberChef/
得到解密的字符串:23152553081a5938126a3931275b0b1313085c330b356101511f105c
# -*- coding:utf-8 -*- from base64 import b64decode key = ‘Flag{This_a_Flag}‘ decode_byte = ‘23152553081a5938126a3931275b0b1313085c330b356101511f105c‘ encode_base64 = ‘‘ lists = [] for i in range(len(decode_byte)//2): lists.append(int(decode_byte[i*2:(i+1)*2],16)) # for i in range(0,len(decode_byte),2): # lists.append(int(decode_byte[i:i+2],16)) print (lists) for i in range(len(lists)): encode_base64 += chr(lists[i] ^ ord(key[i%len(key)])) t = ‘0123456789+/abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ=‘ table = ‘ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz0123456789+/=‘ table = str.maketrans(t, table) flag = b64decode(encode_base64.translate(table)) print(flag)
BJD{0v0_Y0u_g07_1T!}
E8D8BD91871A1E56F53F4889682F96142AF2AB8FED7ACFD5E标签:imp range utf-8 测试 观察 col 获取 base cdecl
原文地址:https://www.cnblogs.com/Mayfly-nymph/p/12347921.html